Exploit Trigger Detection: A new frontier in Application Protection
Application Detection and Response (ADR) technologies are essential for identifying and mitigating runtime attacks. Yet, many existing approaches struggle to detect nuanced, logic-based vulnerabilities effectively.
The recent Next.js vulnerability (CVE-2025-29927), where attackers bypassed authentication using a specific HTTP header (x-middleware-subrequest), underscores the limitations of traditional ADR methods. Commonly used techniques relying on instrumentation or sandboxing frequently miss threats due to operational complexity and insufficient context awareness.

Challenges with Existing CADR:
- Complex deployments involving agent-based instrumentation.
- Limited contextual clarity to differentiate normal from malicious behavior.
- Ineffective detection of subtle, logic-driven exploits by rule-based approaches.
Evaluating Common CADR Approaches:
Several existing CADR methodologies offer varying benefits and limitations:
Instrumentation-based CADR:
- Merits: Provides detailed insights into runtime behaviors; can offer precise detection for known attacks.
- Limitations: High performance overhead, significant operational complexity, and difficulty scaling across diverse environments.
Sandbox-based CADR:
- Merits: Safely evaluates suspicious behaviors by isolating them in controlled environments; effective against explicit malicious payloads.
- Limitations: May overlook subtle logic-based exploits that appear harmless in isolation; often misses vulnerabilities involving legitimate behaviors.
Observability-based CADR:
- Merits: Minimal operational friction; extensive visibility across application runtime behavior without code modification.
- Limitations: Potentially limited contextual depth, making it challenging to accurately classify sophisticated or subtle exploits, potentially resulting in false positives.
Introducing ADR with Exploit-Trigger Defense
Our approach represents a step-change in how runtime threats are detected and mitigated. We call this Exploit Trigger Defense. It focuses on identifying and disrupting the precise execution path that initiates an exploit, before the attacker gains control.
Key capabilities of our Exploit Trigger Defense approach include:
- CVE and Rule-Agnostic Detection: We model normal behavior of packages at runtime to identify anomalies, without requiring preloaded signatures or rule sets.
- Behavioral Sandboxing: Suspicious execution flows are dynamically analyzed in context to determine whether they represent malicious intent.
- Contextual Awareness: We incorporate environment-specific behaviors, such as legitimate network access in frameworks like Next.js, to avoid false positives and detect actual abuse.
- Exploit Trigger Monitoring: When vulnerability context is known, we directly observe the precise execution step that would initiate the exploit. This enables targeted, high-confidence detection.
- Performance-Efficient Runtime Analysis: Our architecture avoids inline instrumentation and delivers continuous runtime insight with minimal system overhead.
- First Action Detection and Response: We identify and intervene on the initial malicious activity in an attack chain, before lateral movement or data access occurs.
Practical Example: Addressing CVE-2025-29927
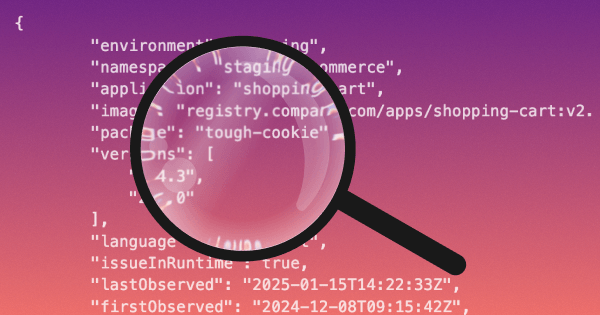
Our system continuously monitors the Next.js authentication middleware function. An exploit attempt using the x-middleware-subrequest header triggers immediate detection, capturing essential details such as:
- The precise HTTP request initiating the exploit.
- The middleware logic was bypassed.
- The unauthorized endpoint accessed.
Our system blocks the malicious request at the first sign of suspicious activity, maintaining normal operation for legitimate users.
The Future of ADR: Contextual Precision
By proactively intercepting exploits and accurately identifying initial malicious actions, our ADR strategy significantly improves detection precision and response effectiveness. Pre-Exploit Intercept and First Action Detection & Response empower security teams to rapidly address advanced, logic-based vulnerabilities with confidence and clarity.
Related blogs
From Reachability to Reality: Proving Vulnerable Code was Executed & Exploited in Production
Memory analysis plays a critical role in turning kernel-level signals into function-level proof of execution. See which vulnerable functions actually run in your environment, cut noise and prioritize risk that exists (and is exploitable) in your running application.
Kodem just built the world’s only Dev to Prod Agentic Taskforce in Cyber
At RSAC 2025, we launched Kai, the first AI-native application security engineer. Today, we’re expanding it into a fully agentic task force that truly performs AppSec tasks from start to finish.

Multi-Agent Architectures: The Next Leap in Application Security
Most security tools today, static analyzers, fuzzers, even single-agent LLMs, struggle to find complex, multi-step vulnerabilities. But the emerging model of multi-agent collaboration can fundamentally transform vulnerability discovery. Argusee’s recent results are just a glimpse of what's possible.
A Primer on Runtime Intelligence
See how Kodem's cutting-edge sensor technology revolutionizes application monitoring at the kernel level.
Platform Overview Video
Watch our short platform overview video to see how Kodem discovers real security risks in your code at runtime.
The State of the Application Security Workflow
This report aims to equip readers with actionable insights that can help future-proof their security programs. Kodem, the publisher of this report, purpose built a platform that bridges these gaps by unifying shift-left strategies with runtime monitoring and protection.
.png)
Get real-time insights across the full stack…code, containers, OS, and memory
Watch how Kodem’s runtime security platform detects and blocks attacks before they cause damage. No guesswork. Just precise, automated protection.

Stay up-to-date on Audit Nexus
A curated resource for the many updates to cybersecurity and AI risk regulations, frameworks, and standards.





