SeCURE your applications with Kodem Remedies

In the rapidly evolving landscape of application development technologies, development and deployment processes continuously become more complex, presenting a myriad of challenges for Application Security teams.
While identifying critical issues with state-of-the-art technologies is crucial, the remediation process for these issues often becomes a bottleneck that requires careful navigation to ensure swift and effective resolution, without causing significant friction within the organization.
In this blog we will explore how Kodem is revolutionizing this process by introducing Kodem Remedies, making it more efficient, less disruptive, and more cost-effective.
The remediation challenge landscape:
1. Significant efforts required
Addressing the most impactful risks, understanding the context and root cause, and determining the necessary actions to mitigate each risk, demand extensive manpower and time. This process requires a substantial investment by both security, DevOps, and development teams.
2. Ineffective use of current tools
The Application and Cloud Security industry offers a significant amount of tools that assist with different parts of the remediation process. Orchestrating these tools effectively within organizational processes is challenging, yet crucial for maximizing the return on investment of security teams and ensuring your organization’s security posture.
3. Lack of remediation processes
The absence of established remediation processes poses a significant challenge for organizations dealing with both zero-day incidents and daily security operations.
During a zero-day incident, the primary goal of the organization is swift issue resolution. This enables the security team to efficiently collaborate with the departments responsible for implementing the necessary fixes. However, when addressing security issues as part of routine operations, the process becomes more intricate and potentially disruptive for the organization.
While some organizations have predefined processes for handling ongoing security tasks, these processes don't always function as anticipated. This mismatch can lead to considerable friction between the development, DevOps, and security teams, hindering the seamless execution of remediation efforts.
4. Addressing security issues
Addressing application security issues is often not an easy task. Identifying the ideal fix for any security issue requires a deep understanding of the application’s dependency graph and supply chain, such as which libraries and images it uses, and how. Having this knowledge will help assess the possible impact and required effort of each fix while avoiding breaking changes as much as possible. This in turn will reduce friction and increase buy-in when prioritizing security fixes among development and security teams.
5. Validating the fixes and tracking the fix updates
After prioritizing the security fixes that are to be addressed, communicating them to the code owners and eventually fixing them, the development and security teams need to validate that the risks were indeed removed. This validation process can be challenging on its own, as the fix may need to be deployed on several environments, such as dev, staging, and production. Hence, effective validation requires that the relevant teams have visibility into various environments.
Who owns remediation?
Traditionally, the responsibility for the Application Security Remediation process lay predominantly with the Application Security team, executed by the development and DevOps teams. However, our observations of organizational processes indicate a notable shift. Security teams are usually short-staffed, which makes collaboration with the development teams crucial. Developers are increasingly becoming active participants in the Security operations and are not only part of the execution.
“Responsibility for remediating exposures and implementing and configuring security controls is shifting from application security leaders to developers.”
According to the Gartner® How to Protect Your Cloud-Native Applications in Production report
The rising popularity of the "you code it, you own it" principle underscores this transformation. This principle emphasizes the shared responsibility of development and DevOps teams within the application security ecosystem. It signifies a collaborative approach where developers are not only executing security measures but also actively contributing to decision-making and remediation processes. This paradigm shift recognizes the crucial role of developers in fostering a secure and resilient application environment.
How Kodem makes remediation simple
At Kodem, we get that fixing things in your organization needs to be straightforward. We help development, DevOps and security teams figure out exactly what needs to be done, where it needs to be fixed, and by whom, ensuring clarity in each step, so everyone can focus on their job and do it well.
What sets Kodem apart is the full and deep application context from Code to Runtime.
First, Kodem knows what truly puts you at risk. Leveraging Runtime Intelligence and comprehensive visibility into your deployed environments, allows Kodem to truly understand the risk impact of each issue on your environment. By bridging the gap between runtime and development, remediations can be prioritized based on their criticality before they are sent to developers to take action.
Second, for each issue found, Kodem can identify and pinpoint the risk source and the required resolution action according to your application's building blocks, dependencies, and owners.
Since Kodem continuously monitors all your application resources, we can easily help you follow the resolutions across your environment, ensuring that a resolved issue is no longer affecting your environment.
“When applications are refreshed and modified so frequently, it is impossible to keep track of vulnerabilities and perform timely remediation with development and runtime application security tools isolated from each other.”
According to the Gartner® How to Protect Your Cloud-Native Applications in Production report
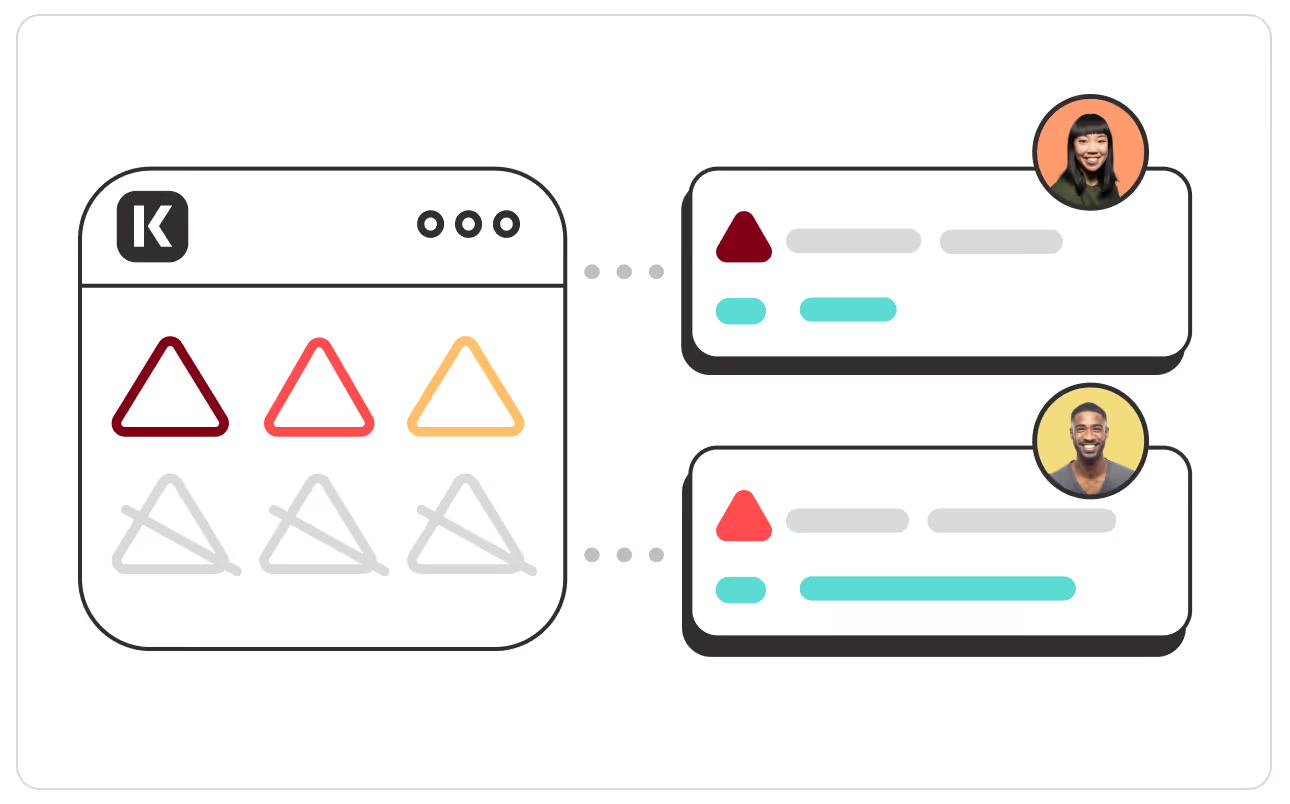
Leveraging the Kodem Code-to-Runtime context, we expertly craft the right remediation capsule for you, named Kodem Remedy. This innovative feature encapsulates the necessary remediation action items by source and owner, allowing you to seamlessly share remediation steps with the relevant teams through the Kodem UI and your organization's ticketing system.
This means that the engineering team no longer needs to waste time on issue prioritization and validation. Instead, they can just log in to Kodem or their favorite ticketing system, view all the remedies that they own, and follow the instructions to resolve them, streamlining the process into their day-to-day routine.
Kodem Remedies automatically determines the root cause, impact, and owner for every issue, utilizing full context from code to runtime. It suggests the ideal fix for your environment and validate that each issue is indeed resolved within your running environments.
Kodem Remedies makes it easier than ever to cure your application.
Gartner How to Protect Your Cloud-Native Applications in Production, 20 November 2023. GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Related blogs
Prompt Injection was Never the Real Problem
A review of “The Promptware Kill Chain”Over the last two years, “prompt injection” has become the SQL injection of the LLM era: widely referenced, poorly defined, and often blamed for failures that have little to do with prompts themselves.A recent arXiv paper, “The Promptware Kill Chain: How Prompt Injections Gradually Evolved Into a Multi-Step Malware,” tries to correct that by reframing prompt injection as just the initial access phase of a broader, multi-stage attack chain.As a security researcher working on real production AppSec and AI systems, I think this paper is directionally right and operationally incomplete.This post is a technical critique: what the paper gets right, where the analogy breaks down, and how defenders should actually think about agentic system compromise.
From Reachability to Reality: Proving Vulnerable Code was Executed & Exploited in Production
Memory analysis plays a critical role in turning kernel-level signals into function-level proof of execution. See which vulnerable functions actually run in your environment, cut noise and prioritize risk that exists (and is exploitable) in your running application.
A Primer on Runtime Intelligence
See how Kodem's cutting-edge sensor technology revolutionizes application monitoring at the kernel level.
Platform Overview Video
Watch our short platform overview video to see how Kodem discovers real security risks in your code at runtime.
The State of the Application Security Workflow
This report aims to equip readers with actionable insights that can help future-proof their security programs. Kodem, the publisher of this report, purpose built a platform that bridges these gaps by unifying shift-left strategies with runtime monitoring and protection.
.avif)
Get real-time insights across the full stack…code, containers, OS, and memory
Watch how Kodem’s runtime security platform detects and blocks attacks before they cause damage. No guesswork. Just precise, automated protection.





