.png)
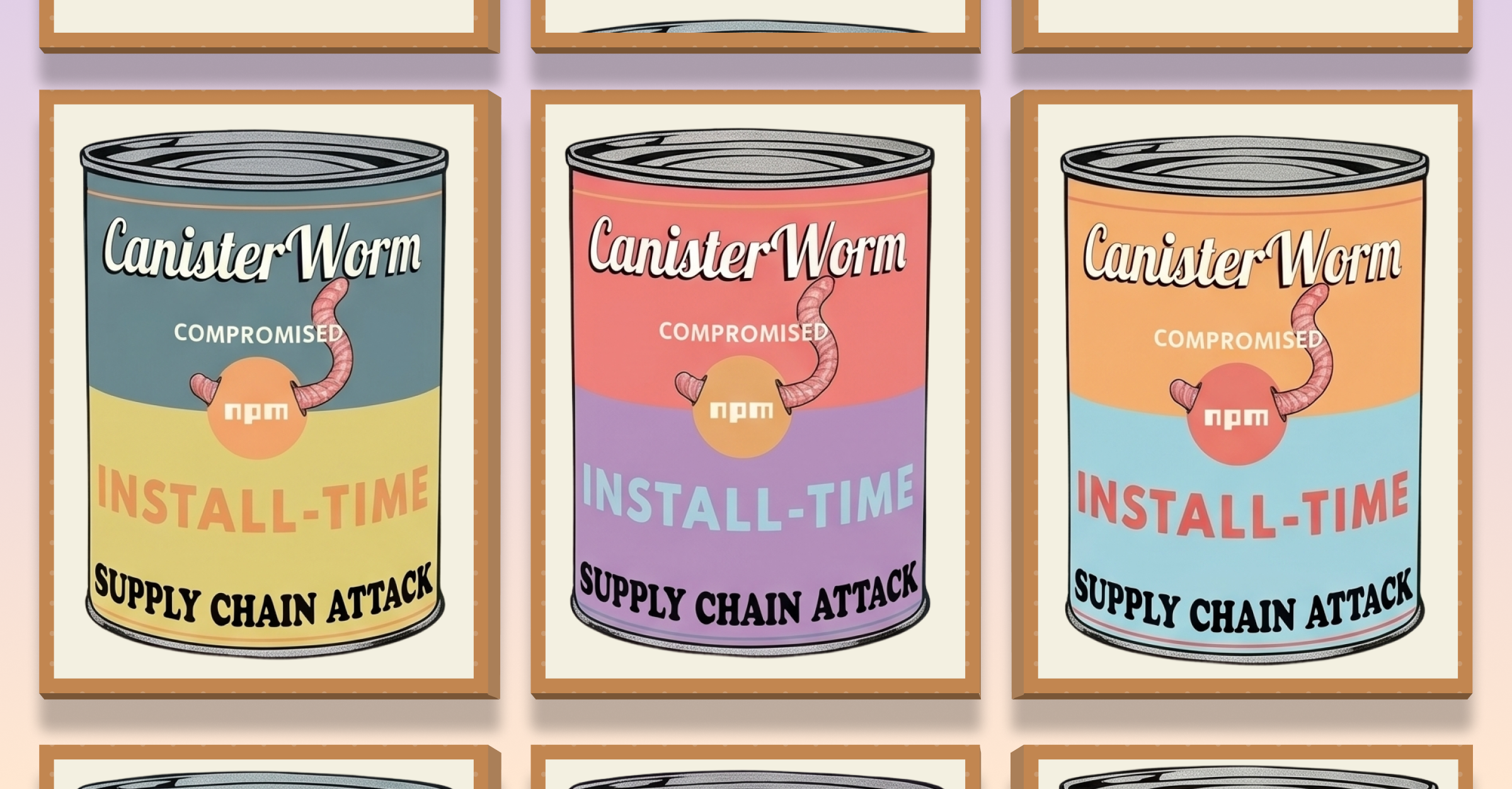
Bitwarden CLI version 2026.4.0 was compromised after attackers gained access to its release pipeline by hijacking a GitHub Actions workflow. This allowed them to publish a tampered package to npm that executed malicious code during installation. The compromise was part of a broader supply chain attack targeting CI/CD workflows and package distribution systems, with shared infrastructure and techniques observed across multiple incidents linked to Checkmarx tooling.
Rather than exploiting an application vulnerability, the attack leveraged trusted developer tooling as the entry point. Since Bitwarden CLI is commonly used to retrieve and manage secrets in CI/CD pipelines and developer environments, the malicious package executed directly in contexts where sensitive credentials were already accessible.
Independent analysis from JFrog and OX Security has identified overlaps in infrastructure, techniques and payload behavior with broader supply chain campaigns, including activity sometimes referred to as TeamPCP and Shai-Hulud, though attribution remains inconclusive.
What Happened
Attackers gained access to the Bitwarden CLI release pipeline by compromising a GitHub Actions workflow and exfiltrating CI/CD tokens. This access allowed them to modify the package before publication and release a malicious version @bitwarden/cli@2026.4.0 to npm.
This access allowed them to:
- Include malicious code in the package contents through a
bw1.jsfile. - Add a
preinstallhook that triggered duringnpm install. - Publish the compromised version through the official npm distribution channel.
During installation, the malicious package executed a preinstall script that deployed a credential-harvesting payload. The payload retrieved and executed additional code, including a bundled runtime, to enumerate and extract sensitive data from the host environment.
The payload targeted credentials and sensitive artifacts already present in the execution environment, including:
- Cloud provider credentials: AWS, GCP, Azure.
- GitHub and npm authentication tokens.
- SSH keys and local configuration files.
- Shell history and developer environment artifacts.
- AI tooling and MCP-related configuration files.
When GitHub tokens were discovered, the malware used them to inject malicious GitHub Actions workflows into accessible repositories. This enabled further extraction of CI/CD secrets and created a path for lateral movement across pipelines and projects.
Collected data was encrypted with AES-256-GCM and exfiltrated to attacker-controlled infrastructure audit.checkmarx[.]cx. If primary exfiltration failed, data was committed to attacker-controlled GitHub repositories as a fallback channel.
Since the package was distributed through the official npm registry, it executed within trusted environments, including developer machines and CI/CD pipelines where credentials were already available.
The malicious version was available for approximately 93 minutes before removal. Despite the short exposure window, installations occurred in both developer environments and automated pipelines, increasing the likelihood of credential exposure and downstream compromise.
What This Incident Shows
This attack reinforces a shift in how supply chain compromises operate:
- The entry point is no longer the application: Attackers are targeting build pipelines and developer tooling, where trust is implicit and protections are weaker.
- Installation is execution: The use of preinstall hooks turns dependency installation into an execution vector, allowing code to run before any application logic is invoked.
- Credentials are the real objective: The goal is not persistence within the package, but access to tokens and secrets that enable lateral movement across CI/CD systems.
- One installation can expand the blast radius: A single compromised developer environment can expose tokens that allow attackers to modify pipelines, access repositories and propagate further.
- Trusted distribution channels amplify impact: Publishing through npm ensures the malicious code runs inside environments that already have privileged access.
What’s Affected
- Bitwarden CLI npm package:
@bitwarden/cli@2026.4.0 - Developer environments where the CLI was installed locally.
- CI/CD pipelines using Bitwarden for secrets retrieval and automation.
Only environments that installed or updated to version 2026.4.0 during the exposure window are at risk (April 22, 2026, 5:57 PM - 7:30 PM ET).
Immediate Actions
- Identify exposure scope: Locate installs of
@bitwarden/cli@2026.4.0across developer machines, CI/CD pipelines and automation workflows. - Remove compromised version: Uninstall
@bitwarden/cli@2026.4.0and clear the npm cache before reinstalling the verified version 2026.4.1. - Rotate credentials immediately: Bitwarden, npm, cloud providers: GitHub, AWS, GCP and Azure and any tokens stored or accessed on affected systems.
- Review for unauthorized activity: Audit GitHub Actions workflows, CI/CD logs and repository activity for:
- Unexpected workflow changes.
- New or modified automation jobs.
- Suspicious outbound connections.
- Limit credential exposure in CI/CD: Restrict token scope, avoid long-lived credentials and restrict automation permissions for workflows.
The Broader Pattern
This incident follows a recurring supply chain pattern: attackers compromise build and release pipelines to distribute trusted software as the delivery mechanism.
Instead of exploiting application code, they:
- Gain access to CI/CD and release workflows.
- Inject code into trusted artifacts.
- Publish through official distribution channels.
- Execute inside environments where secrets are already accessible.
This pattern has been observed across multiple campaigns targeting CI/CD systems, developer tooling and package registries.
The Bottom Line
The Bitwarden CLI incident underscores a fundamental shift in supply chain threats: the focus has moved from exploiting code vulnerabilities to compromising trusted execution paths.
Risk is now defined not just by a package's contents, but by its operational context. Since this tool executed within environments that already contained highly sensitive credentials, a single installation served as a gateway for extensive compromise. Consequently, security strategies must evolve beyond identifying potential vulnerabilities; they must prioritize monitoring what code actually runs, the environment in which it executes and its access at runtime.
References
- Bitwarden Community Forums. April 23, 2026. Bitwarden Statement on Checkmarx Supply Chain Incident. Bitwarden.
- BleepingComputer. April 23, 2026. Bitwarden CLI npm Package Compromised to Steal Developer Credentials. BleepingComputer.
- Endor Labs. April 23, 2026 The Bitwarden CLI Supply Chain Attack: What Happened and What to Do. Endor Labs.
- JFrog. April 23, 2026.TeamPCP Campaign Spreads to npm via a Hijacked Bitwarden CLI. JFrog.
- OX Security. April 23, 2026. Shai-Hulud: The Third Coming — Bitwarden CLI Backdoored in Latest Supply Chain Campaign. OX.
- SecurityWeek. April 24, 2026. Bitwarden NPM Package Hit in Supply Chain Attack. SecurityWeek.
- SC Media. April 24, 2026. Checkmarx supply chain hack impacts Bitwarden CLI. SC Media.
- The Hacker News. April 23, 2026. Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign. The Hacker News.
Related blogs
The NIST NVD update changes vulnerability management more than most teams realize
NIST’s April 15, 2026 update to NVD operations is easy to summarize and easy to underread. The headline change is familiar by now: NIST will continue listing all CVEs, but it will only immediately enrich a subset, prioritizing CISA KEV, software used within the federal government, and software covered by Executive Order 14028’s critical software definition.
7
CanisterSprawl: What’s at risk, and what to do next
The campaign tracked as CanisterSprawl is a supply chain intrusion in which malicious npm package versions execute at install time, harvest credentials from developer environments, exfiltrate that material to attacker-controlled infrastructure and then attempt to republish poisoned packages using stolen publisher tokens.
4

Adobe Reader Zero-Day Exploited Through Malicious PDFs
A zero-day vulnerability in Adobe Reader was actively exploited for several months through malicious PDF files. The campaign allowed attackers to steal sensitive data, fingerprint victims, deliver follow-on payloads and potentially achieve arbitrary code execution and full system compromise.
3
A Primer on Runtime Intelligence
See how Kodem's cutting-edge sensor technology revolutionizes application monitoring at the kernel level.
Platform Overview Video
Watch our short platform overview video to see how Kodem discovers real security risks in your code at runtime.
The State of the Application Security Workflow
This report aims to equip readers with actionable insights that can help future-proof their security programs. Kodem, the publisher of this report, purpose built a platform that bridges these gaps by unifying shift-left strategies with runtime monitoring and protection.
.png)
Get real-time insights across the full stack…code, containers, OS, and memory
Watch how Kodem’s runtime security platform detects and blocks attacks before they cause damage. No guesswork. Just precise, automated protection.




