When Vulnerabilities Come From Images You Don’t Own
Runtime visibility for third-party container images and the missing context for ownership and remediation.

Modern applications increasingly rely on third-party container images. While these components accelerate application development, they also introduce external security risks that complicate ownership, prioritization, and remediation. A key struggle is determining ownership, prioritizing risk and efficiently remediating externally introduced vulnerabilities.
Security tools frequently detect vulnerabilities within these images but often fail to provide the essential context required for action. This lack of context slows triage, obscures ownership and delays remediation efforts, leaving critical questions unanswered:
- Which applications are affected by the vulnerability?
- Did the vulnerability originate from internal code or a vendor image?
- Who is responsible for the remediation?
- What’s the correct path for the fix, from line-level code changes to verified dependency and image upgrade paths?
- Is the vulnerable component actively utilized during runtime?
Runtime-aware identification of third-party image risk offers the necessary context to accelerate triage and remediation.
The Visibility Gap in Third-Party Images
Containerized environments introduce a complex, layered dependency structure:
Application > Container > Base Image > Third-Party Components > Open Source Packages
Vulnerabilities found in runtime can originate from various points in this chain:
- Application dependencies.
- Base images.
- Third-party vendor images.
- Nested dependencies within images.
Conventional scanning tools identify these vulnerabilities but fail to distinguish their true origin. Consequently, security teams receive findings without critical context, such as:
- The source of the vulnerability.
- The team or entity responsible for its ownership.
- The appropriate remediation path.
This lack of context results in significant operational friction. Security teams are forced to spend time on investigation rather than focused remediation. Developers are assigned tickets for issues they didn’t introduce and don’t own. Platform teams inadvertently inherit risk.
Why Third-Party Images are Hard to Secure
Managing third-party container images presents distinct technical complexities:
- Layered image architecture.
- Transitive open-source dependencies.
- Images maintained by external vendors.
- Unknown or irregular patch cycles.
- Usage of shared infrastructure.
Vulnerabilities can originate deep within image layers:
Vendor Image > Base Image > Package in Runtime > Application
This deep origin makes it exceptionally difficult to:
- Pinpoint the exact origin of the vulnerability.
- Accurately track the scope of exposure.
- Assign clear ownership for the component.
- Determine the correct remediation steps.
The complexity is further amplified when these images are reused across multiple different services and deployment environments.
The Operational Problem: Ownership and Remediation
Once vulnerabilities are identified, a critical question remains:
- Who owns the fix?
- Is the fix the responsibility of the development team, including for example patching dependencies?
- Does the platform team need to update base images?
- Should DevOps rebuild containers?
The Impact of Unclear Ownership: a lack of clarity on who is responsible for remediation leads to significant problems:
- Inefficiency: Tickets become bouncing balls between teams.
- Increased Risk: Remediation slows down, allowing risk to accumulate.
- Weakened Compliance: Overall governance suffers.
This ownership challenge is particularly critical with widely adopted vendor images, which often power multiple applications simultaneously. Common examples include infrastructure components such as NGINX, Redis, Postgres, MongoDB and RabbitMQ, which consistently rank among the most downloaded official container images on Docker Hub.
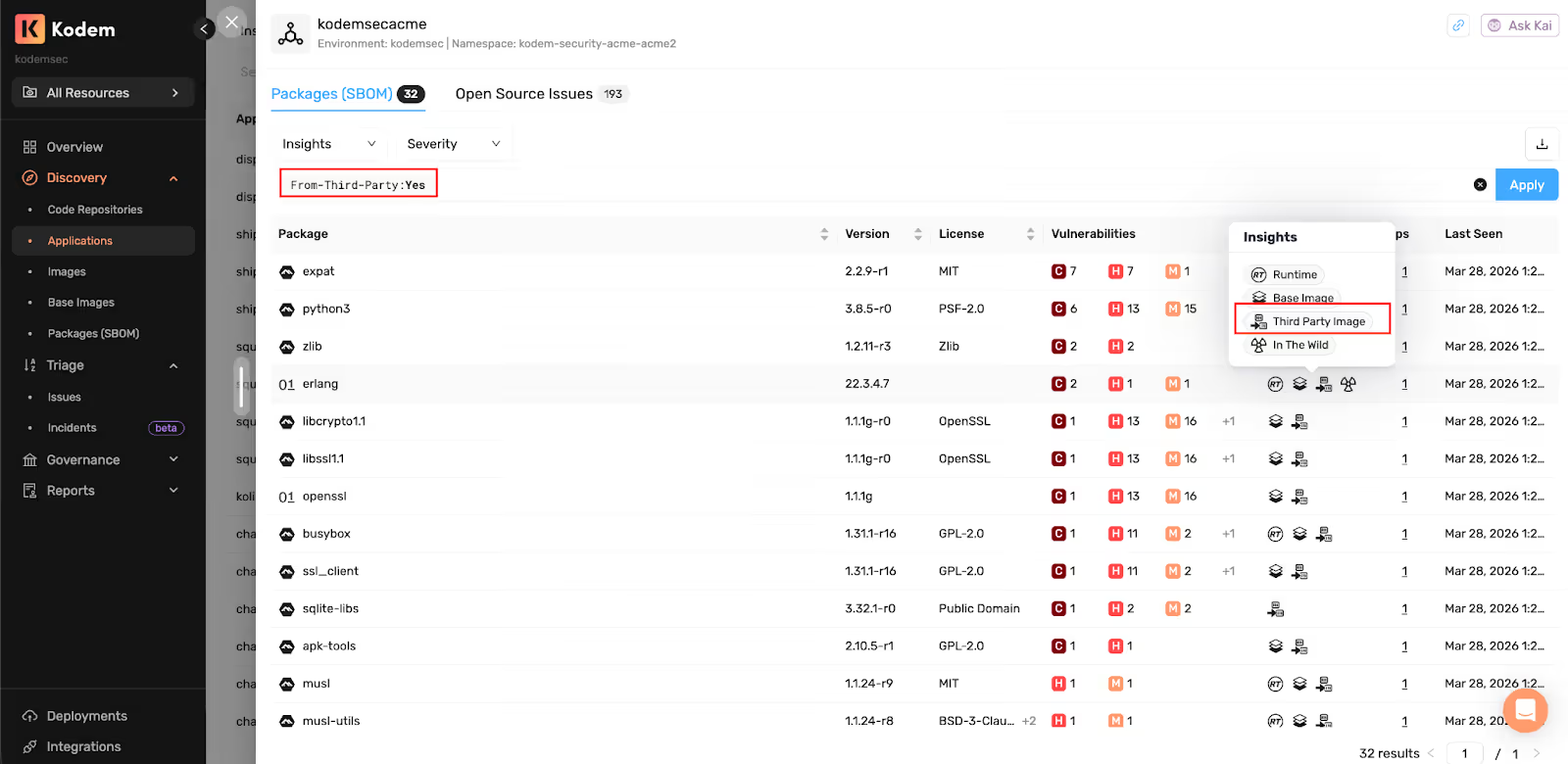
Runtime-Aware Third-Party Image Identification
Runtime-aware security shifts the focus from image-only vulnerability identification to a more comprehensive model. By incorporating runtime monitoring, this approach enables:
- Mapping vulnerabilities to runtime workloads: Linking identified vulnerabilities directly to the operational environments where they are executed.
- Attribution and Lineage: Tracing vulnerabilities back to their source in third-party images and tracking the full lineage and origin of those images.
- Identification of Affected Applications: Clearly showing which applications are impacted by the vulnerabilities.
This approach correlates runtime telemetry, image metadata, dependency mapping, and application context: runtime telemetry, image metadata, dependency mapping and application context. Specifically, runtime sensors correlate container metadata, package execution and workload context to accurately identify vulnerabilities introduced by third-party images, map them to the affected applications, and pinpoint their origin and impacted environment.
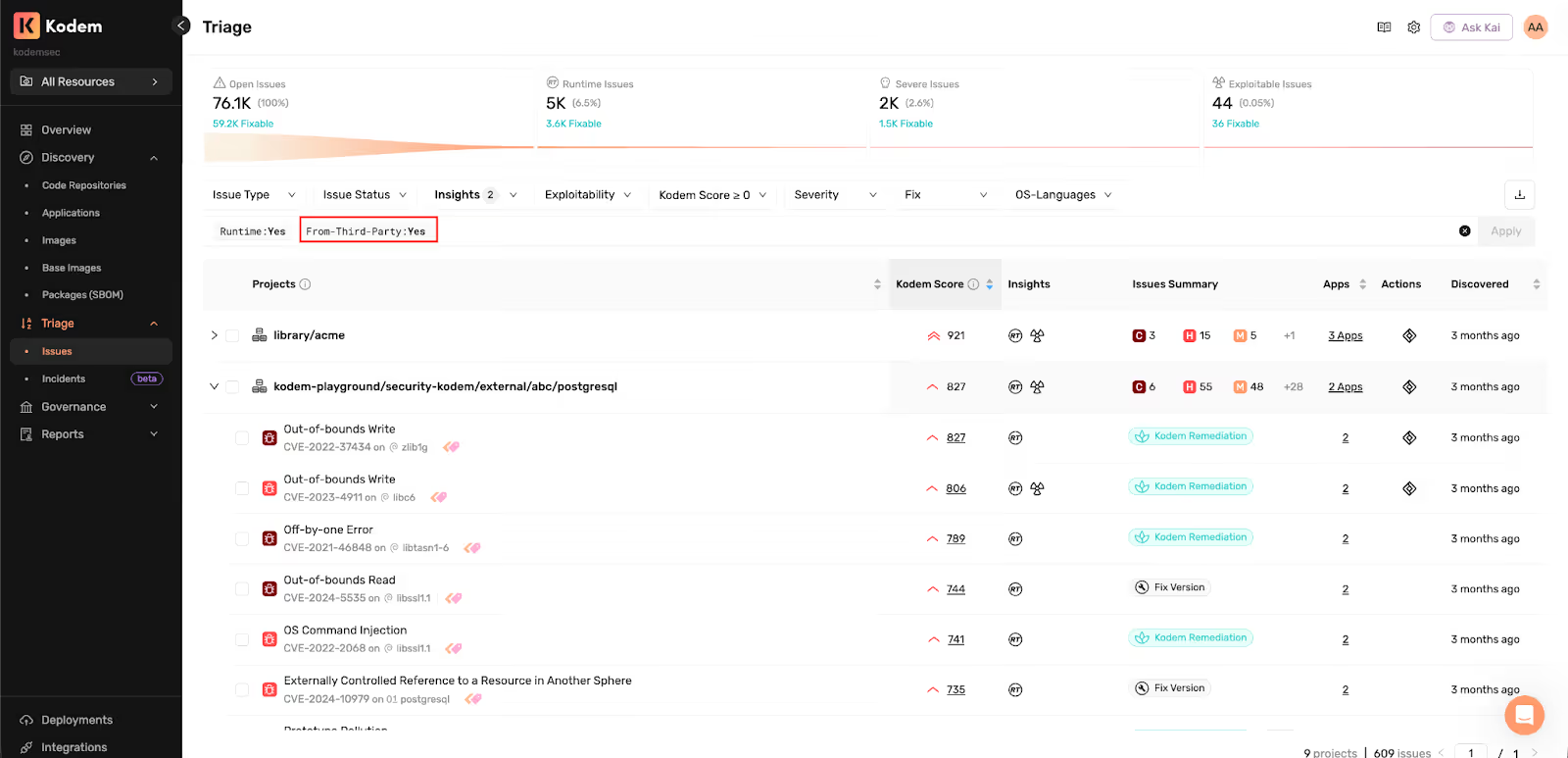
Filtering Applications From Third-Party Images
Once third-party image attribution is established, security teams can:
- Filter applications derived from third-party images.
- Identify affected services.
- Prioritize applications with runtime-observed vulnerabilities.
- Focus remediation on impacted applications.
This shifts triage from all vulnerabilities across infrastructure to applications affected by third-party runtime risk. This is particularly valuable in application environments where:
- Multiple applications share images.
- Platform services run vendor containers.
- Infrastructure risk spreads across workloads.
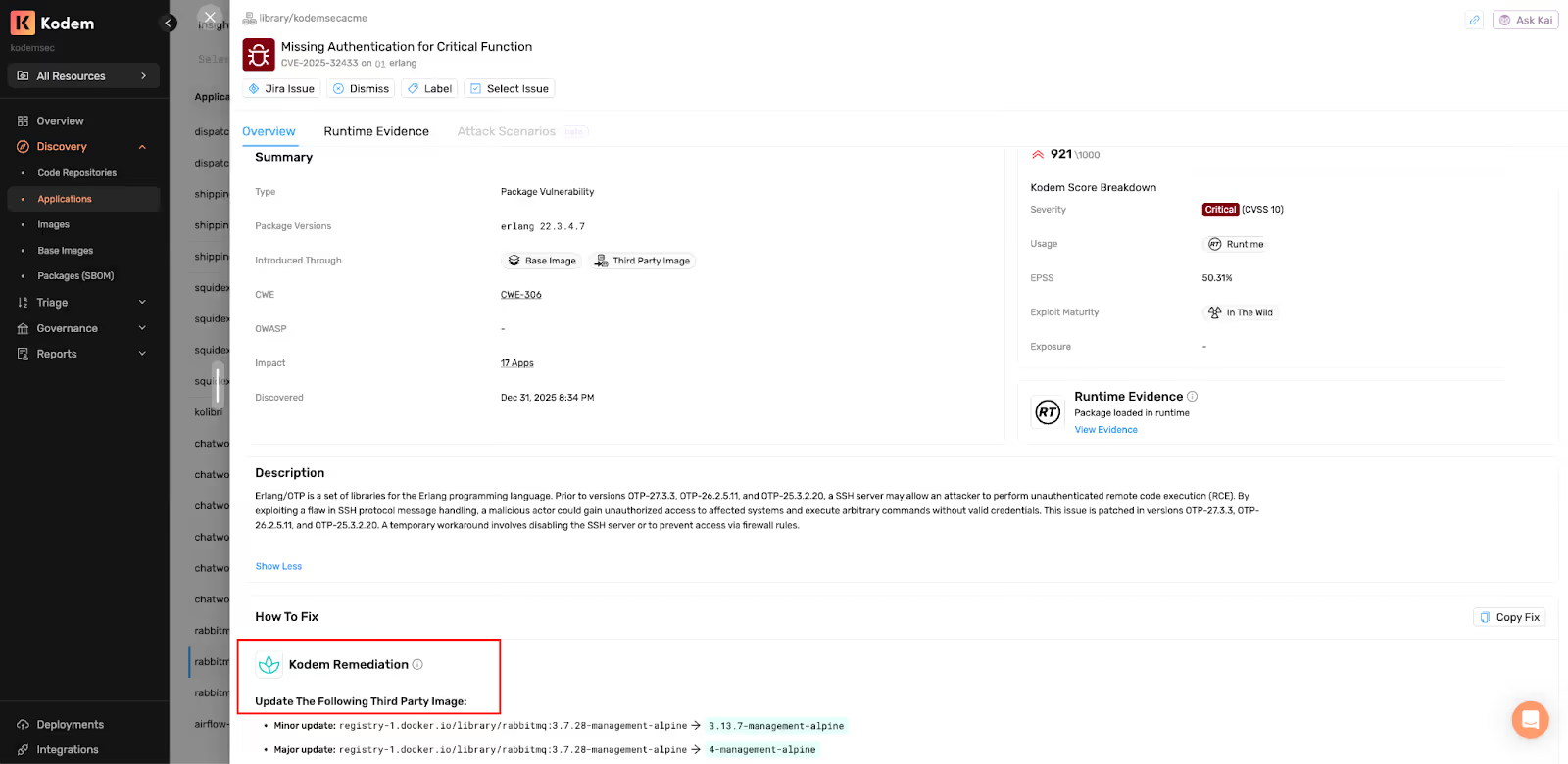
From Visibility to Remediation
Runtime-aware visibility into third-party images transforms security findings into actionable context, enabling teams to pinpoint:
- Vulnerabilities stemming from vendor images.
- Applications affected by third-party components.
- Packages loaded and executed in runtime.
- Dependency invocation details.
- Image lineage and hierarchy.
- Impacted environments.
- Clearly defined ownership boundaries.
- The precise location for remediation efforts.
Identifying vulnerabilities is only the starting point. Effective remediation requires precise guidance. Runtime-aware remediation guidance provides:
- Contextualized vendor image upgrade recommendations
- Semantic version–based upgrade paths (patch, minor, major)
- Correlation of publicly available fixes with runtime-observed components
- Base image update guidance and dependency ownership clarity
This transforms generic public fixes into contextualized remediation guidance, helping teams confidently resolve issues. This approach replaces generic suggestions with image-specific remediation guidance aligned with vendor-maintained updates. The resulting benefits include:
- Faster patching cycles
- Increased developer productivity
- Higher remediation accuracy
Governance Automation
By automating the identification of new or modified open-source issues that pose a third-party image risk, organizations can significantly improve security operations. Once this vendor-derived risk is identified, workflow automations can operationalize it, enabling security teams to prioritize and address the risks effectively. This automation facilitates security governance through key features, including:
- Automated ticket creation.
- Webhooks for seamless integrations.
- Labels to manage notifications.
Ultimately, this process transforms the security team's posture from one of time-consuming, reactive investigation to an efficient, automated operational response.
Runtime Evidence and Image Lineage
Teams can enhance their security posture by utilizing runtime context, which shifts the focus from static image scans to actual execution. This approach provides key data points, such as evidence of package execution, loaded dependencies, image hierarchy, and base image lineage. Ultimately, this leads to faster investigations, more accurate exploitability analysis, and improved risk prioritization.
Why This Matters for Modern Infrastructure
Third-party container images power critical infrastructure across modern environments. When vulnerabilities originate from vendor images, multiple applications may be impacted simultaneously. Runtime-aware attribution provides the context needed to identify ownership, prioritize risk, and confidently remediate.
Turning Insight into Action
Third-party container images accelerate development but introduce external risk into runtime environments. For effective security, simple detection is insufficient; comprehensive visibility, clear ownership, and precise remediation guidance are essential.
By bridging the gap with runtime-aware third-party image identification, you transform standard vulnerability detection into actionable, focused security operations.
Related blogs
Agentic AI Security: WAF + Runtime Defense as an AI Governance Control
How Kodem’s agentic AI security pairs WAF with runtime security to defend vibe coded apps, supply chain worms, and ISO 42001 controls.
6
.avif)
Your AppSec Backlog Has a Shortcut. Here's How to Find It.
When your backlog has thousands of open findings, the question becomes: "What single action gives me the most risk reduction for the least effort?"
5
Securing Vibe Coding: Security for AI-Generated Development
AI coding assistants are reshaping how software is written. Developers increasingly rely on models to read repositories and generate or modify files directly inside local projects, often introducing dependencies, configuration changes and large sections of application logic.
3
A Primer on Runtime Intelligence
See how Kodem's cutting-edge sensor technology revolutionizes application monitoring at the kernel level.
Platform Overview Video
Watch our short platform overview video to see how Kodem discovers real security risks in your code at runtime.
The State of the Application Security Workflow
This report aims to equip readers with actionable insights that can help future-proof their security programs. Kodem, the publisher of this report, purpose built a platform that bridges these gaps by unifying shift-left strategies with runtime monitoring and protection.
.avif)
Get real-time insights across the full stack…code, containers, OS, and memory
Watch how Kodem’s runtime security platform detects and blocks attacks before they cause damage. No guesswork. Just precise, automated protection.





