Your AppSec Backlog Has a Shortcut. Here's How to Find It.
When your backlog has thousands of open findings, the question becomes: "What single action gives me the most risk reduction for the least effort?"
.avif)
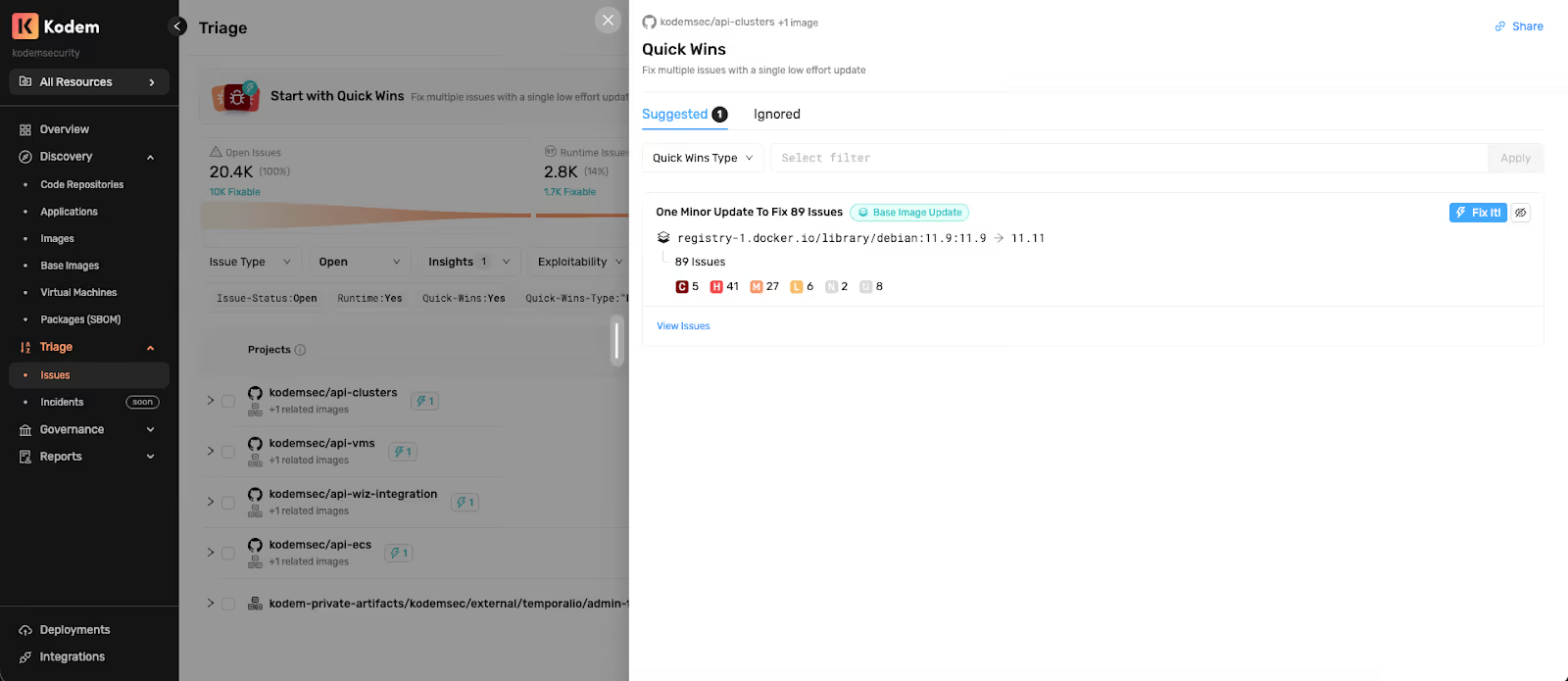
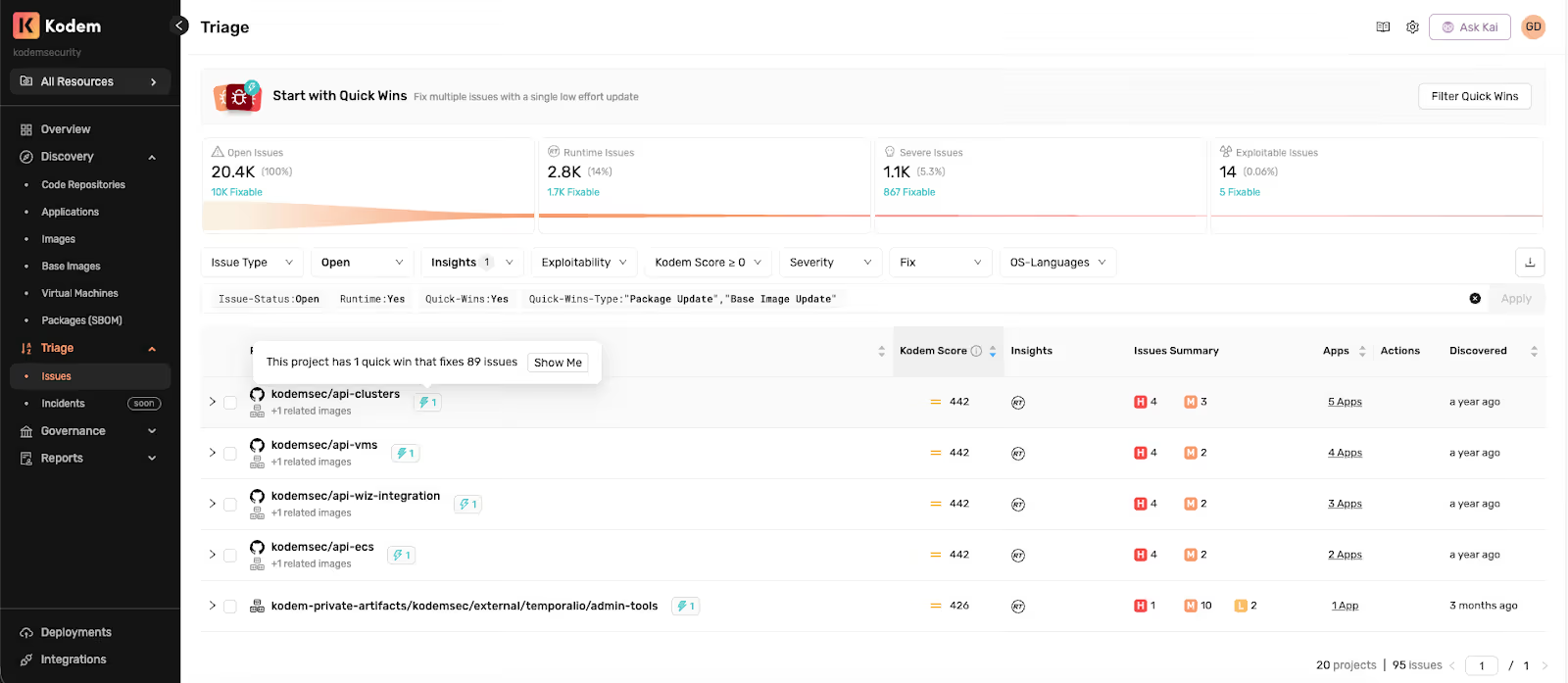
When your backlog has thousands of open findings, the question becomes: "What single action gives me the most risk reduction for the least effort?" Quick Wins answers that by identifying where groups of CVEs can be resolved by a single dependency upgrade or base image update. Each Quick Win is prioritized by combined Kodem Score, which factors in runtime context, reachability and exploitability so your highest-ROI fixes also target your most exposed attack surface.
The Remediation Paralysis Problem
Most AppSec managers live with hundreds or thousands of findings that are real, fixable and worth addressing, but not urgent enough to jump the queue individually. The typical triage workflow is linear: project by project, issue by issue. Without a clear framework, findings accumulate into background noise. Developers see 200 open tickets and stop taking any of them seriously. The CISO asks for MTTR numbers and gets a shrug.
That's where a different kind of leverage comes in, knowing where a single action yields disproportionate impact across the rest of your backlog.
From Fix Versions to Actual Fixes
Most tools stop at telling you a vulnerability was fixed in version X. However, knowing the fix version isn't the same as knowing how to implement the fix.
- Which source file introduced the dependency: package.json, Dockerfile or a transitive chain three layers deep?
- Is the vulnerable package a direct dependency you control or pulled in through a base image?
- Does updating it require one change or five?
Kodem's remediation engine traces every issue back to its origin; the specific source file, the entry point into your environment and the dependency path that brought it in. From there, it determines the fix: not just "upgrade to version Y" but exactly which file to change, whether it's a direct or transitive dependency and the smallest version bump that resolves it. For base images, it matches variants so you don't accidentally switch from bullseye-slim to alpine and break your build.
This is the foundation Quick Wins is built on. Without knowing the true origin and true fix for each issue, you can't reliably group them. With it, you can confidently say: "These 30 issues all trace back to one line in one file, and one patch-level update clears them all."
The Hidden Structure in Your Backlog
Here's something most tools don't surface: in modern software supply chains, a single root dependency is often responsible for dozens of distinct CVEs across multiple services. jackson-databind, lodash, spring-core - these packages show up in nearly every enterprise codebase, and a single version bump can wipe out an entire category of risk.
The same applies to base images. A container built on node:18.15-slim might carry hundreds of known vulnerabilities that all disappear with a minor tag bump - no code changes, no breaking APIs, no sprint planning required. This structure already exists in your data, it just hasn't surfaced as an actionable plan.
Completing the Prioritization Picture
Risk-based prioritization gives you the context to answer the hardest question: "What's actually dangerous in my environment, and what should I fix first?" Quick Wins completes the picture by answering the next question: "Now, what's the most efficient way to shrink everything else?"
Instead of asking "which vulnerability should I triage next?", Quick Wins asks: "which single update resolves the most remaining risk with the least effort?"
Kodem continuously analyzes your open issues and groups them by their root fix - the specific package or base image update that eliminates them. Only Patch and Minor version upgrades that resolve multiple high-severity findings from a single source file qualify. Major version bumps, ambiguous multi-source fixes, and theoretical upgrade paths are excluded entirely. Because each Quick Win is scored using the combined Kodem Score - which reflects runtime reachability and exploitability - the results naturally surface fixes that target real, confirmed risk in your environment, not just the longest CVE list.
The result is a prioritized list of high-ROI actions, each one a concrete instruction: "Update package X from version A to version B in this file. This resolves 12 issues, including 3 Critical and 5 High severity findings."
Think of it as two complementary lenses: risk-based prioritization for your most dangerous findings, Quick Wins for your most efficient fixes. Together, they give your team a complete remediation strategy - address the highest-risk items first, then systematically clear the long tail.
Why This Matters for Every Role
For AppSec: Control Without Micromanagement
The biggest drain on an AppSec manager's time isn't finding risks - it's routing them. Figuring out which team owns which dependency, writing up context for each ticket, following up when nothing happens. Quick Wins compresses that cycle. Instead of filing 12 separate tickets for 12 CVEs, you hand a developer one instruction that clears all of them. You go from ticket router to strategic advisor.
Quick Wins also strengthens your prioritization story. Your top risks are handled through risk-based triage. For the rest, you have a defensible answer: "This single update reduces our open finding count by 15% across 4 production services - and it's a patch-level change." That's a metric that resonates in a boardroom.
For Developers: The Path of Least Resistance
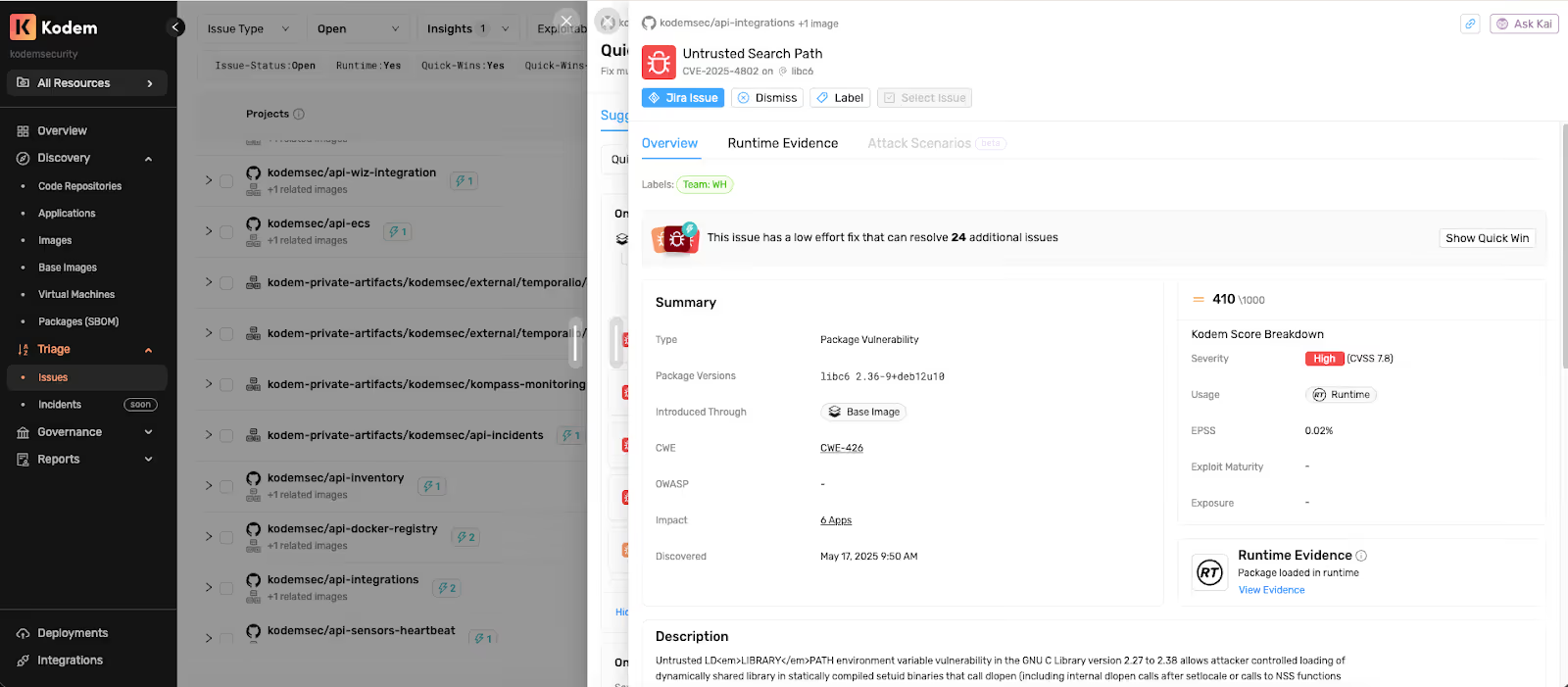
Developers don't resist security work because they don't care. They resist it because it's usually poorly scoped. A ticket that says "CVE-2024-XXXX in lodash - please fix" leaves the developer to figure out: which version to upgrade to, which file to change, whether it'll break anything, and whether it's even running in production.
Quick Wins removes that friction entirely. Each win specifies the exact source file, the current and target versions, and the update type (Patch or Minor). Click "Fix It" and a ready-to-use remediation instruction is on your clipboard. No research, no guesswork, no context switching. Security becomes a scoped task instead of a research project.
For the CISO: Measurable ROI on Remediation
CISOs care about two things: are we getting safer, and are we spending wisely? Kodem's risk-based prioritization gives your team the context to tackle the most dangerous issues first. Quick Wins ensures that beyond those top risks, remediation effort is spent where it has the most impact - targeting findings with high Kodem Scores that reflect runtime-confirmed, reachable, exploitable risk. When a handful of patch-level updates - each taking minutes to apply - measurably reduce your CVE count across multiple production services, that's operational ROI you can put in a quarterly review.
[Video]: https://youtu.be/aPzhq2hDl1M
What Makes a Good Quick Win
Not every fixable issue qualifies. Quick Wins applies strict thresholds to ensure every recommendation delivers meaningful CVE reduction:
- Maximum CVE reduction: Must resolve multiple issues, including at least one High or Critical severity finding.
- Significant combined Kodem Score: Because Kodem Score accounts for runtime reachability and exploitability, this ensures Quick Wins target findings that represent real, confirmed risk in your environment - not just theoretical exposure.
- Patch and Minor versions only: No major version bumps. While these upgrades follow semantic versioning conventions and are expected to be backward-compatible, we recommend standard testing before deploying any dependency update. The focus is maximizing risk reduction, not guaranteeing compatibility.
- Unambiguous fix path: One dependency, one source file, one clear action. If a fix requires coordinating changes across multiple sources, it's excluded.
Every recommendation should be a clear win - a single change that demonstrably reduces your open finding count. That clarity is what makes developers act on them.
It's the difference between handing a developer a spreadsheet of 500 remaining CVEs and handing them a list of 8 updates that eliminate 60% of them.
Related blogs
Agentic AI Security: WAF + Runtime Defense as an AI Governance Control
How Kodem’s agentic AI security pairs WAF with runtime security to defend vibe coded apps, supply chain worms, and ISO 42001 controls.
6

When Vulnerabilities Come From Images You Don’t Own
Runtime visibility for third-party container images and the missing context for ownership and remediation.
4
Securing Vibe Coding: Security for AI-Generated Development
AI coding assistants are reshaping how software is written. Developers increasingly rely on models to read repositories and generate or modify files directly inside local projects, often introducing dependencies, configuration changes and large sections of application logic.
3
A Primer on Runtime Intelligence
See how Kodem's cutting-edge sensor technology revolutionizes application monitoring at the kernel level.
Platform Overview Video
Watch our short platform overview video to see how Kodem discovers real security risks in your code at runtime.
The State of the Application Security Workflow
This report aims to equip readers with actionable insights that can help future-proof their security programs. Kodem, the publisher of this report, purpose built a platform that bridges these gaps by unifying shift-left strategies with runtime monitoring and protection.
.avif)
Get real-time insights across the full stack…code, containers, OS, and memory
Watch how Kodem’s runtime security platform detects and blocks attacks before they cause damage. No guesswork. Just precise, automated protection.




