
Cloud telemetry reveals where a workload is running and the context of the infrastructure. AppSec needs a different layer of evidence: runtime observability that helps determine whether a vulnerability is truly exploitable based on how the application behaves within its environment.
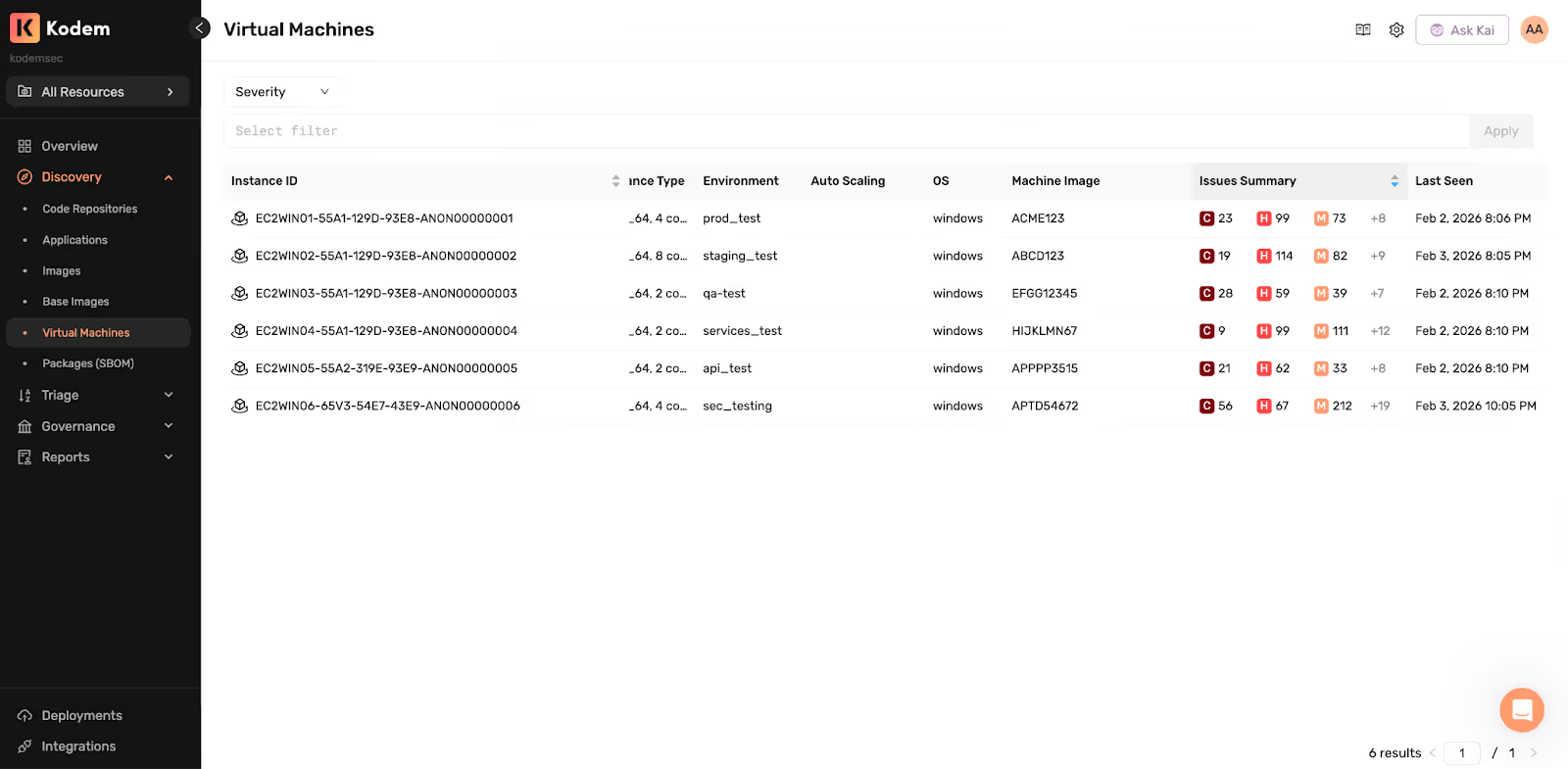
This is especially important in Windows environments, where many business-critical applications still run in architectures that aren’t always compatible with the Linux and container-centric assumptions that shaped much of modern runtime security tooling.
The Operational Reality
Windows carries meaningful application load in most enterprises today. Stable internal services, packaged applications, middleware, long-running .NET services, background jobs and platform components often continue to run on Windows for sound operational reasons.
Today, Windows security teams have the ability to inventory their application assets, however struggle to confirm the execution of applications and therefore cannot confirm the true exposure on their workloads. Most teams can answer:
- Is this package present?
- Is this vulnerability relevant in theory?
What is harder to answer is what actually happened at runtime:
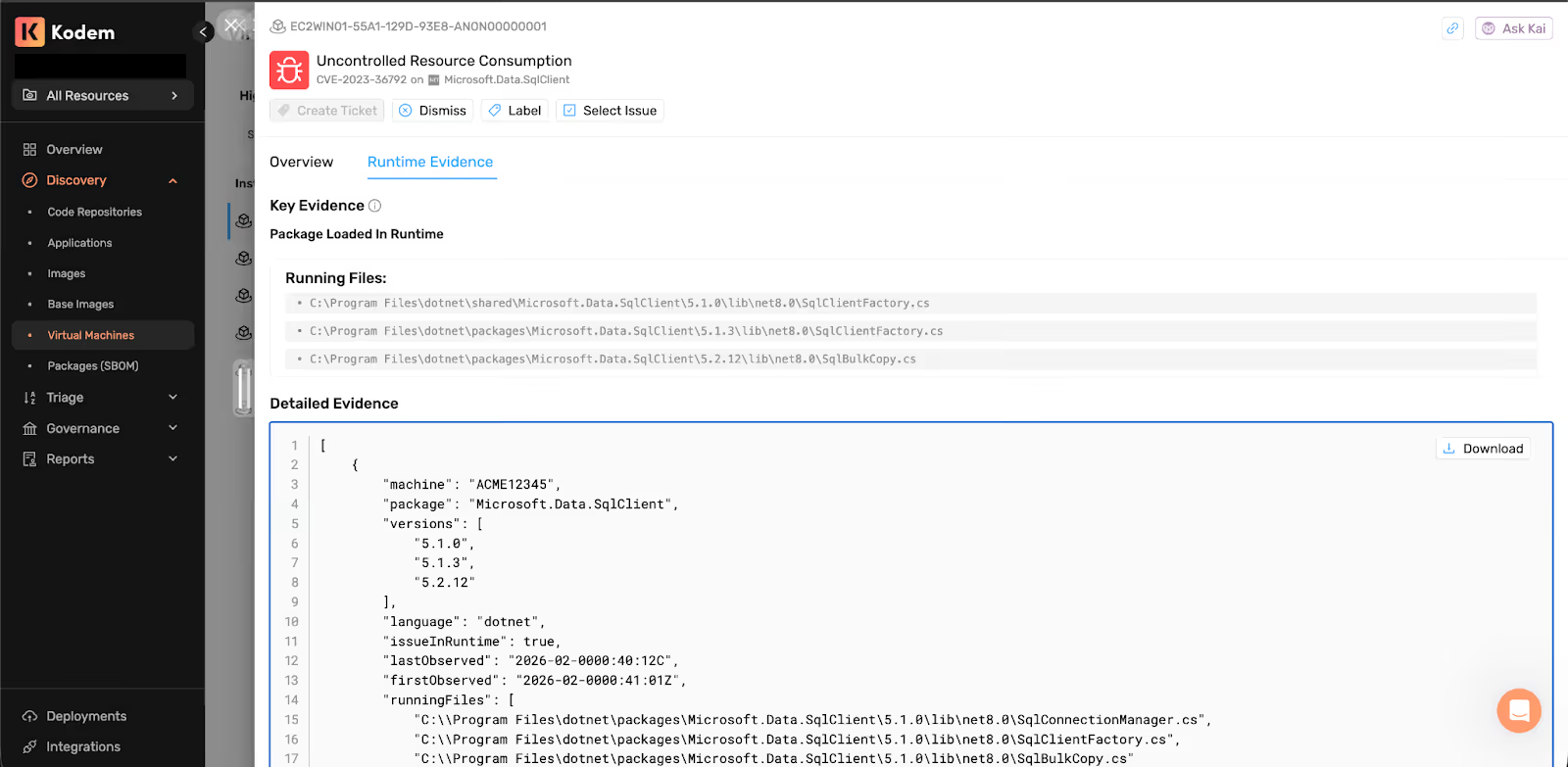
- Was the vulnerable code loaded into a running process?
- On which machine?
- When?
- Under which executable?
- Is it exposed to a public facing IP?
- Is the evidence strong enough to hand to engineering without guesswork?
Why Runtime Context Matters & Why Reachability isn’t Enough
Static analysis and posture signals often oversimplify risk. A package may exist in a base image without ever being used in the application’s actual execution path. Runtime-validated composition, which shows which vulnerable components were actually in use during execution, is critical for SCA findings. Unlike static package inventory, which only lists what is included in an image or dependency tree, this dynamic approach offers a more precise view.
Different Telemetry & Event Sources
Linux innovation accelerated around kernel tracing, often eBPF-based. Windows relies on different event and instrumentation models. The collection method changes, but the requirement for AppSec does not. Security teams still need full-stack application context that shows what resource introduced the vulnerable issue, what was loaded into memory, what ran, what was actually called, and why that changes exploitability.
Memory-Informed Runtime
Effective AppSec runtime systems need more than event observation; they require enough system state, such as executed processes, loaded files and changes over time to interpret event meaning.
Kodem approaches this by combining event tracing, continuous system-state modeling, memory analysis and snapshot-aware change tracking to produce runtime evidence that’s traceable to a specific machine and timeframe. That model is valuable because it correlates source-code findings, dependency context, binary evidence, and runtime behavior rather than treating each layer as a separate signal.
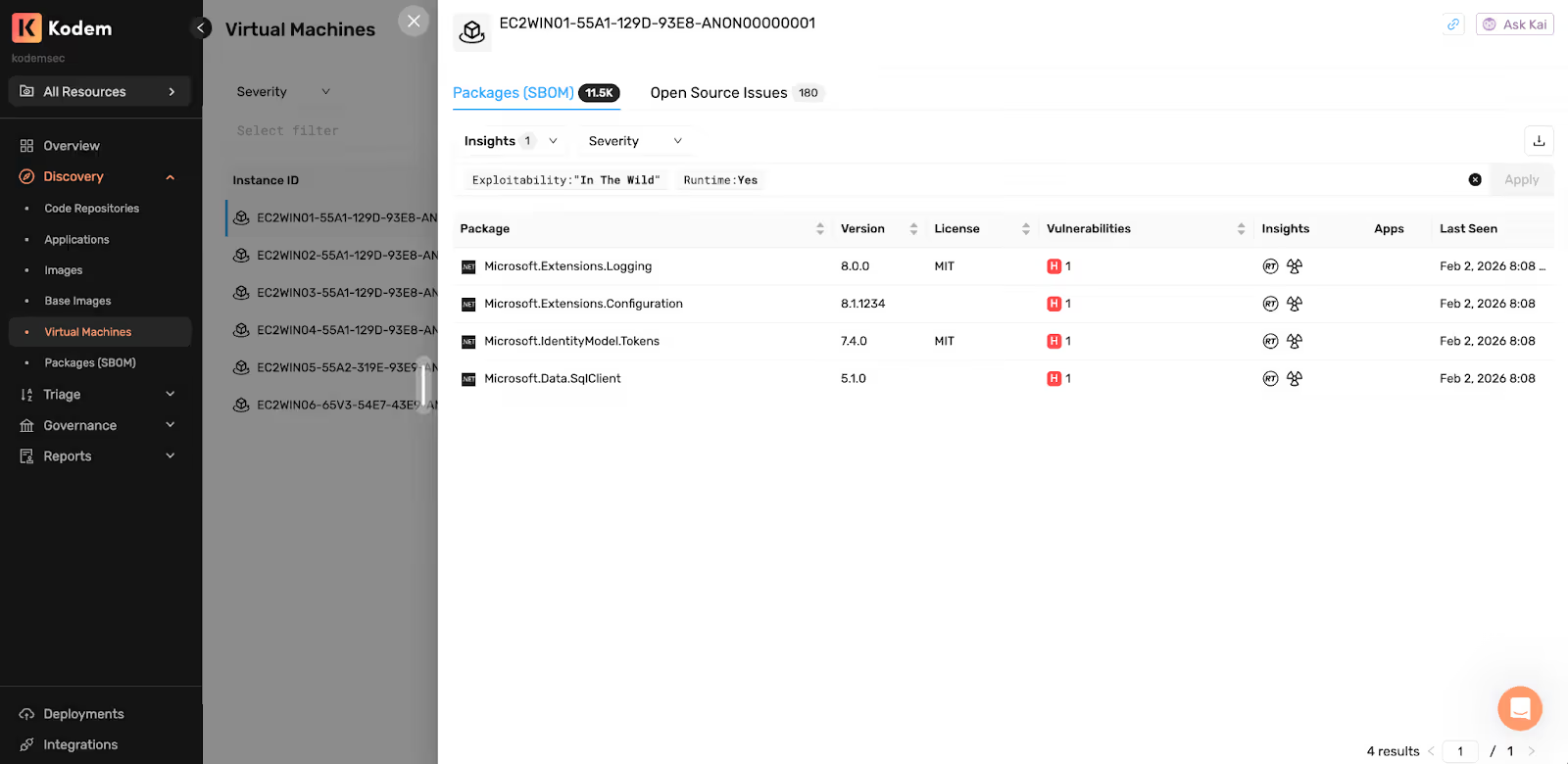
While collection mechanisms vary across Linux, Windows and macOS, the proof model for AppSec should remain consistent: what was observed in use, what was loaded, what executed, what was called and where it happened.
Cloud telemetry can be valuable at describing infrastructure context. AppSec teams still need proof inside the running workload. The closer your signal gets to application behavior, the less you have to infer.
Why This Matters in Mixed Environments
Even in standardized infrastructure, many organizations still run mixed environments where containers and virtual machines coexist, Linux runs alongside Windows, and some critical or legacy services remain non-containerized for operational reasons.
Runtime evidence has to remain equally meaningful across those systems. If the depth of proof varies by platform or deployment model, prioritization becomes inconsistent and teams end up grading risk by environment rather than by observed behavior.
Why Windows Runtime AppSec Completes the Model
Windows makes this gap easier to see because it often sits at the intersection of long-running services, stable deployments and deep dependency chains that provide clear visibility with partial confidence into what is present, but weaker proof of what actually ran.
The requirement, however, is broader than Windows. The real objective is a consistent, execution-aware AppSec model that preserves meaningful runtime evidence across operating systems and deployment models. That is where runtime context matters most: showing what was actually in use inside the running applications, beyond the exposure and surrounding context that cloud and infrastructure telemetry can describe.That evidence improves trust in the signal by reducing the need to repeatedly re-validate whether a finding is truly relevant, giving teams higher-confidence prioritization based on observed application behavior rather than static possibility or surrounding context alone.
Related blogs
Agentic AI Security: WAF + Runtime Defense as an AI Governance Control
How Kodem’s agentic AI security pairs WAF with runtime security to defend vibe coded apps, supply chain worms, and ISO 42001 controls.
6
A Primer on Runtime Intelligence
See how Kodem's cutting-edge sensor technology revolutionizes application monitoring at the kernel level.
Platform Overview Video
Watch our short platform overview video to see how Kodem discovers real security risks in your code at runtime.
The State of the Application Security Workflow
This report aims to equip readers with actionable insights that can help future-proof their security programs. Kodem, the publisher of this report, purpose built a platform that bridges these gaps by unifying shift-left strategies with runtime monitoring and protection.
.avif)
Get real-time insights across the full stack…code, containers, OS, and memory
Watch how Kodem’s runtime security platform detects and blocks attacks before they cause damage. No guesswork. Just precise, automated protection.





.avif)

